CVE-2020-13958 - Breakdown
In the simplest of terms, CVE-2020-13958 is an issue with OpenOffice where, upon opening specially crafted documents, a program or webpage can be opened with no user interaction required.
PoC
I will use the original authors words to explain it because they explain it best:
The problem is, the product does not handle script:event-listener handlers as macro execution (like LibreOffice does). Using a construct like this:
<office:scripts>
<office:event-listeners>
<script:event-listener script:language="ooo:script"
xlink:href=".uno:OpenHyperlinkOnCursor" script:event-name="dom:load"/>
</office:event-listeners>
</office:scripts>
One can trigger opening URLs without any confirmation dialogs in OpenOffice, including special .uno or .service link handlers that were designed for internal use only.
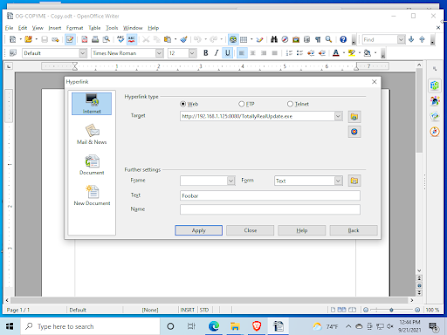
An illustration of the hyperlink issue can be seen below:
As shown, it uses file:/// to open an executable as soon as the document is opened. But this alone isn't enough to cause major issues, there has to be a malicious file already on the PC for this to work well. Can we chain two commands together in the file path, such as calling cmd.exe and then passing a string to it?
Looks like the answer to this is a resounding "No."
What about downloading a file and then opening it? Well it opens the first hyperlink fine, but can't run the executable afterwards. OpenOffice seems to only run the first hyperlink regardless of what's in the second one, such as another download link. That's another "No."
So how can we change this slightly to work better?
Chaining with a macro
This is where chaining it with a macro comes in. We can change the original idea a little and, instead of opening an executable on the persons computer, we can open a weblink and automatically trigger a download for a new file, maybe an "update" for OpenOffice - to steal an idea from some common Microsoft Office malware.
We will change the URL to, instead of a local file, automatically bring us to a download page for an "update" for OpenOffice.
And then add a macro to run:
And then set it to run on document close:
Now when the document is opened it redirects to another webpage that prompts the user to download an "update" and then, on document close, the exe we downloaded runs. This takes a little bit of tricking the user to work properly, we have to make them believe that when the document is opened their version of OpenOffice is out of date, prompting them to allow the download through. Then once the download is complete and the document closes, smartscreen will stop the file from running without a user clicking yes, but even without a signing cert a good amount of users will click "More info" -> then "yes" to allow the exe to run.