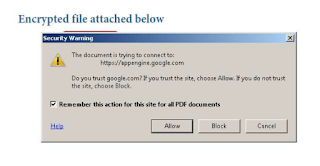
It was a PDF that had a hyper link in it to click.
The link went to appengine.google.com - a pretty innocuous URL. Anyone would trust it. It's Googles cloud compute platform.
However, it pivoted off of there to a malicious webpage using URL flags.
The whole URL looked like https://appengine.google.com/_ah/logout?continue=https://www.maliciousdomain.com
What's more worrying though is that by clicking it, you were prompted if you trusted the parent domain in the URL - Google. Not the URL it redirects to once you've clicked the link.
This is worrying - especially considering that Google just moved last Spring to stop domain fronting.
Additionally, only one engine on VirusTotal flagged this as malicious - Kaspersky.
Update 10/2/2018
This attack vector is currently being used by Emotet. AlienVault USM was able to detect multiple threats attempting to utilize this to trick users into following malicious links.
Update 3/19/2019 - This has been patched out by Google